richard.chetwynd | December 14th, 2017
If you’re using Slack, chances are you’re no stranger to posting notifications and useful information from various other apps and systems into your Slack channels.
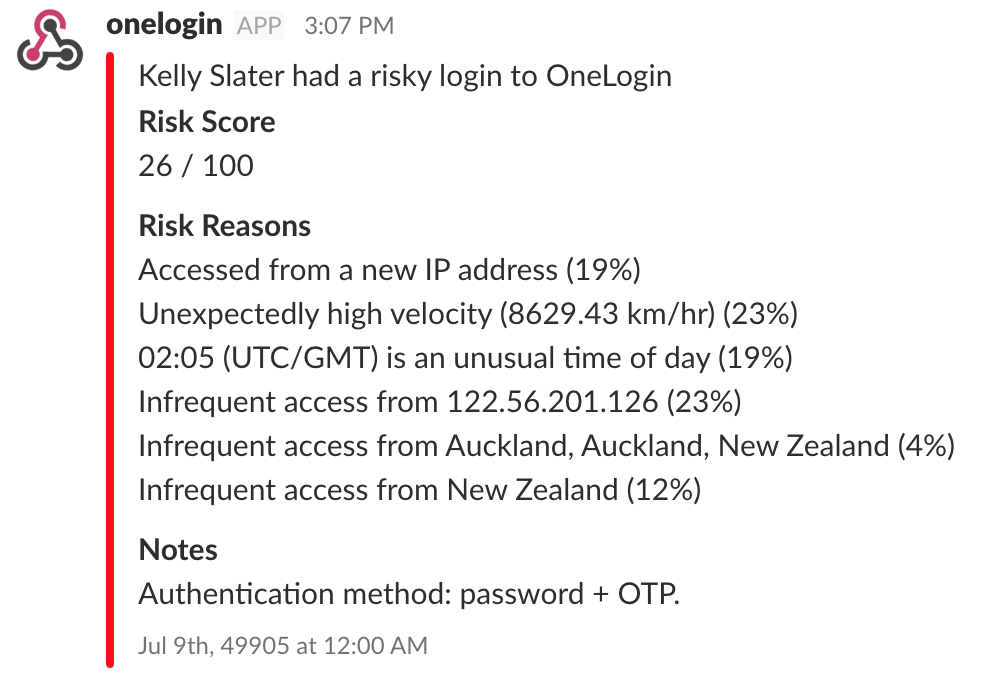
In this post I’ll show you how to send login events that have an elevated risk to a Slack channel. This is a great way to keep an eye out for suspicious access, and you could easily extend this code sample to send other types of events.
Event Webhooks
At OneLogin we recently released Webhooks which make it possible to make event driven decisions in your applications. The webhook system is like a firehose of the activity in your OneLogin account, so the best way to make use of it is be selective about the types of events that you want to respond to.
In this sample we will be using the “User Log In” event combined with a “Risk Score” that is calculated each time a user logs in.
Note that the Risk Score we use in this sample will only be populated for customers that make use of our Adaptive Authentication feature. As a side note, the benefit of Adaptive Auth is that it only prompts users for a second authentication factor or one time password when an elevated level of risk is detected for a log in.
Getting Started
Ok, so let’s get this show on the road. It’s actually very simple thanks to the awesome work the Serverless team has done to make deploying Lambda functions and API Gateway configuration to AWS. You could easily adapt this sample app and deploy it to Azure or other cloud providers, but for this example I’m using AWS.
Step 1: Setup AWS Credentials
In order for Serverless to deploy this sample to AWS, you will need AWS CLI tool installed and configured with credentials that have access to create/manage API Gateway and Lambda functions. Read more about setting up AWS CLI.
Step 2: Create a Incoming Webhook on Slack
In order to send a notification to a Slack channel, we need to get an endpoint from Slack that we can post messages to. They call this an Incoming Webhook and you can add one to your Slack account here.
Once you have your Incoming Webhook setup, grab the Webhook Url that they issue you.
It will look something like this: https://hooks.slack.com/services/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
Step 3: Deploying the app via Serverless framework
Now for the fun part. First up if you don’t have it already, get Serverless installed on your local machine. It only takes a minute to setup and will give you a cli tool for creating and deploying serverless apps.
Once you have serverless installed, you can pull the sample code for this app from Github.
> git clone git@github.com:onelogin/serverless-onelogin-slack.git
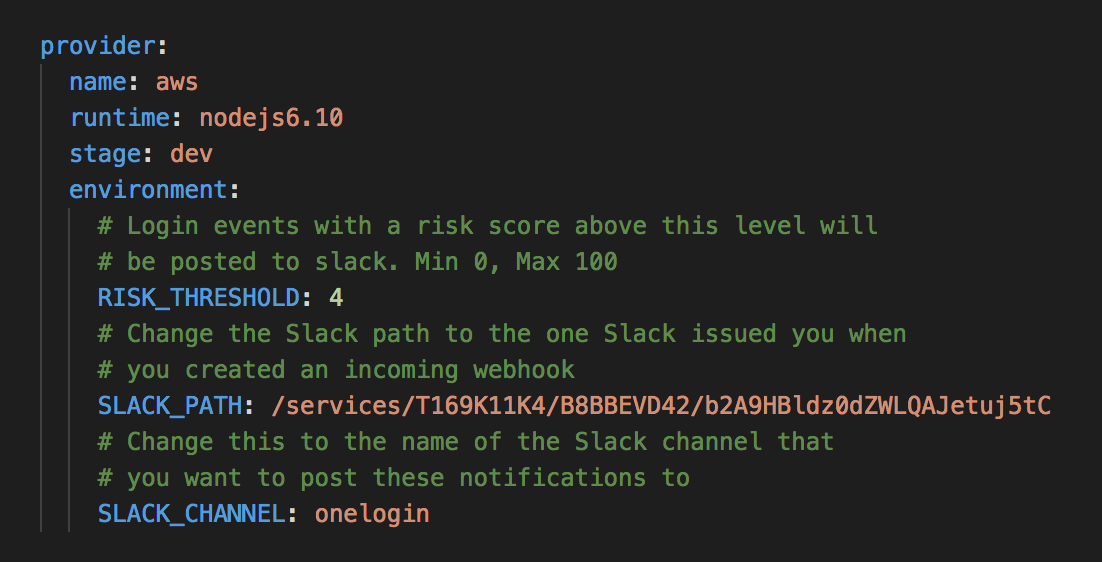
Next, we will tweak the configuration with your own Slack endpoint. So open up “src/serverless.yml” and change SLACK_CHANNEL and SLACK_PATH to your own values.
With those simple configuration changes made, you’re now ready to deploy the app.
Open your terminal and move into the “src” directory then enter the following:
> serverless deploy
Serverless will now package up the code and send it to AWS. It takes a couple of minutes the first time around and should eventually return a successful response.
At this point you have successfully deployed a serverless app and you just need to get the public endpoint for it that will listen for events from OneLogin. To do this, run:
> serverless info
Which will return a POST endpoint url for your new function. Save this url for use in the next step.
Step 4: Setup OneLogin Event Broadcaster
Lastly, you will use the endpoint url to register against an Event Broadcaster in your OneLogin account. Do this via the OneLogin Admin portal in the Activity > Event Broadcaster area.
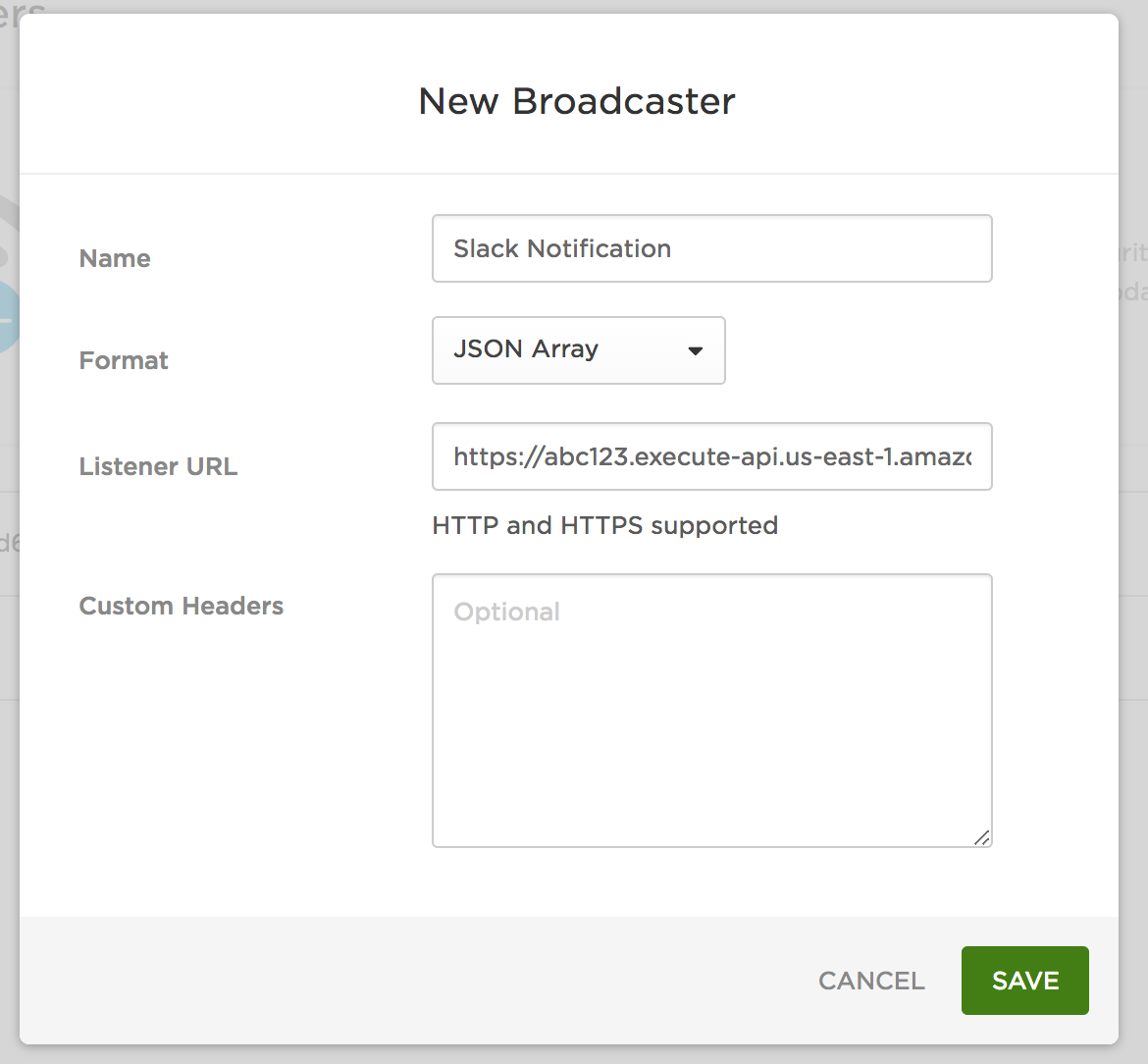
Set the Listener Url using your serverless endpoint url and change the Format to JSON Array.
Step 5: Test your work
At this point you’re all done and risky login notifications will start posting to your nominated Slack channel.
Now try logging into OneLogin while mixing up some of your normal behaviors like using a different browser and coming in via VPN etc. The default RISK_THRESHOLD setting in your app is pretty low so these small changes should create enough risk to push the notifications through to Slack.
Remember you need to have Adaptive Authentication enabled on the user policy for your test user.
Extending the sample
This is really just a quick sample of one way that you can make use of Event Webhooks from OneLogin. If you want to try different levels of risk just tweak the RISK_THRESHOLD in your serverless.yml and then deploy the app again with “serverless deploy”.
Webhooks are an incredibly powerful feature so hopefully you can use this app as base for more advanced integrations to improve security and automate workflows.
And if you’re interested in learning more about Adaptive Authentication, click here to get a demo.
